How Do Financial Data Centers Ensure Data Security?
Financial data centers handle vast amounts of sensitive information daily. Ensuring the security of this data is paramount to maintaining customer trust and compliance with regulatory requirements. Financial institutions must safeguard against cyber threats, insider risks, and physical breaches by adopting robust security measures. This article explores the core challenges faced by financial data centers and the advanced technologies and best practices they implement to ensure data security.

What Are the Core Security Challenges in Financial Data Centers?
Growing Cyber Threats and Vulnerabilities
Financial data centers are prime targets for cybercriminals due to the valuable information they hold. These centers consistently face phishing attacks, ransomware, and other sophisticated threats. Protecting against these vulnerabilities requires staying ahead in the cybersecurity landscape, continuously monitoring for threats, and frequently updating security protocols.
Regulatory Compliance Requirements
Operating within the financial sector involves adhering to stringent regulatory standards such as GDPR, PCI DSS, and SOX. These regulations mandate comprehensive security measures to protect consumer data and financial records. Navigating this complex regulatory environment necessitates meticulous attention to compliance requirements and regular auditing to avoid hefty penalties and legal repercussions.
Insider Threats and Human Errors
Internal risks, including accidental data leakage and deliberate actions by disgruntled employees, pose significant threats to data security. Human errors, such as misconfigured security settings, can also create vulnerabilities. Mitigating these risks involves implementing strict access controls, monitoring employee actions, and conducting regular training to maintain high security awareness.
Advanced Technologies for Data Security in Financial Data Centers
Encryption and Data Masking Techniques
Encryption ensures that data remains secure during transmission and storage. Data is transformed into an unreadable format, which can only be decrypted by authorized parties. Data masking, on the other hand, hides actual data with fictional information, safeguarding sensitive data during non-production environments.
AI-Powered Threat Detection Systems
Artificial Intelligence (AI) plays a crucial role in identifying and mitigating security threats in real-time. AI systems analyze vast amounts of data to detect unusual patterns and predict potential breaches. These systems can flag anomalies quicker than traditional methods, significantly reducing response times and minimizing potential damage.
Multi-Factor Authentication (MFA) and Access Control
Multi-Factor Authentication (MFA) enhances security by requiring users to verify their identities through multiple credentials, such as passwords, biometrics, or security tokens. Coupled with stringent access control mechanisms, MFA ensures only authorized personnel can access sensitive data, reducing the risk of unauthorized access.
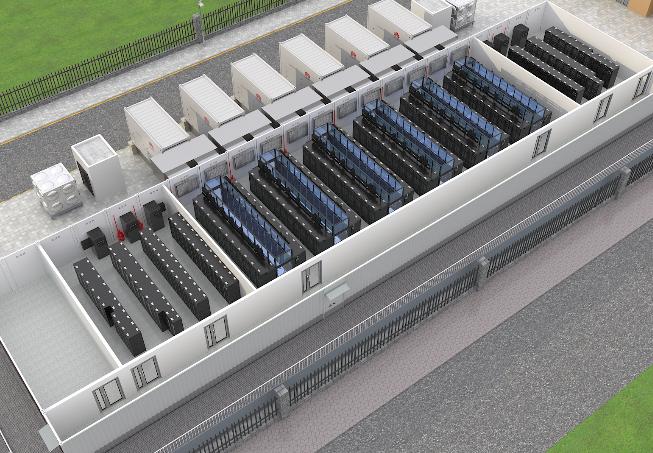
Physical Security Measures in Financial Data Centers
Biometric Access Systems
Physical security at financial data centers often includes biometric authentication methods such as fingerprint scans, facial recognition, and retinal scans. These measures add an extra layer of security by ensuring that only authorized personnel can gain entry to restricted areas within the data center.
Surveillance and Monitoring Solutions
Continuous surveillance through strategically placed cameras and monitoring systems is vital for maintaining security. These systems help detect and deter unauthorized access, ensuring real-time response to any security breaches. Monitoring also includes environmental controls such as temperature and humidity sensors to protect data integrity.
Disaster Recovery and Redundancy Plans
Disaster recovery plans are essential for ensuring data availability and integrity in the event of natural disasters, power outages, or other emergencies. Redundancy plans involve duplicating critical data and systems in multiple locations. Regular testing and updating of these plans guarantee quick recovery and continuity of operations during unforeseen events.
Best Practices for Ensuring Data Security in Financial Data Centers
Regular Security Audits and Penetration Testing
Conducting routine security audits and penetration testing helps identify and fix vulnerabilities before they’re exploited. These proactive steps ensure security protocols stay effective, up-to-date, and aligned with the latest threats and compliance standards, safeguarding your systems and data from potential breaches.
Employee Training and Awareness Programs
Educating employees on security protocols and data protection is vital. Regular training reinforces best practices, empowering staff to act as the first line of defense against cyber threats. This minimizes human error and enhances overall organizational security, ensuring a proactive approach to safeguarding sensitive information.
Implementing Zero Trust Architecture
Zero Trust Architecture operates on the principle of “never trust, always verify,” requiring strict identity verification for every person and device attempting to access the network, regardless of whether they are inside or outside the network perimeter. This approach significantly reduces the risk of unauthorized access and data breaches.
Conclusion
Securing financial data centers involves a multifaceted approach that addresses both digital and physical threats. By leveraging advanced technologies, maintaining strict access controls, and adhering to regulatory standards, financial institutions can protect sensitive data effectively. Continuous vigilance and proactive measures ensure that data security remains robust, safeguarding both the institution’s integrity and customer trust.